Cannot connect to a database because of SSLHandshakeException
warning
Due to Java security policy, TLS 1.0 and TLS 1.1 protocols are disabled and considered insecure.
Due to Java security policy, the usage of TLS 1.0 and TLS 1.1 protocols was disabled. This Java update caused the javax.net.ssl.SSLHandshakeException error that occurred when you tried to connect to old servers that still accept these protocols.
As a fix, you can explicitly enable these protocols. Note that it might result in vulnerability issues. Consider using newer versions of TLS.
Open data source properties. You can open data source properties by using one of the following options:
Navigate to File | Data Sources....
Press CtrlAltShift0S.
In the Database Explorer ( View | Tool Windows | Database Explorer), click the Data Source Properties icon (
).

Select a data source for which you want to enable disabled algorithms (for example, MySQL 8.0.3). The following required algorithms might be disabled:
SSLv3,TLSv1,TLSv1.1,RC4,DES,MD5withRSA,DH keySize < 1024,EC keySize < 224,3DES_EDE_CBC,anon,NULL,include jdk.disabled.namedCurves.In the right pane of a data source, click Test Connection.
In the notification, select an action that you want to perform. You can select among the following actions:
Edit disabled algorithms: opens the Advanced tab of the selected data source and moves the focus to the VM options field. In the VM options field, you can edit a list of disabled algorithms manually (for the
Djdk.tls.disabledAlgorithmsoption).Enable TLSv1: removes
TLSv1from theDjdk.tls.disabledAlgorithmsoption. This action will enable TLS 1.0.Enable TLSv1.1: removes
TLSv1.1from theDjdk.tls.disabledAlgorithmsoption. This action will enable TLS 1.1.Enable all protocols in JDBC driver: removes
SSLv3,TLSv1,TLSv1.1,RC4,DES,MD5withRSA,DH keySize < 1024,EC keySize < 224,3DES_EDE_CBC,anon,NULL,include jdk.disabled.namedCurvesfrom theDjdk.tls.disabledAlgorithmsoption. This action enables all the disabled algorithms.
Click Test Connection and see if the fix works.
You can try Enable TLSv1 and Enable TLSv1.1 first. If the error still occurs, try to enable other algorithms.

In a file browser, create a custom.java.security file with the following contents:
jdk.tls.disabledAlgorithms=SSLv3, RC4, DES, MD5withRSA, \ DH keySize < 1024, EC keySize < 224, 3DES_EDE_CBC, anon, NULL, \ include jdk.disabled.namedCurvesNote that TLSv1 is removed from the list of disabled algorithms.
Open data source properties. You can open data source properties by using one of the following options:
Navigate to File | Data Sources....
Press CtrlAltShift0S.
In the Database Explorer ( View | Tool Windows | Database Explorer), click the Data Source Properties icon (
).

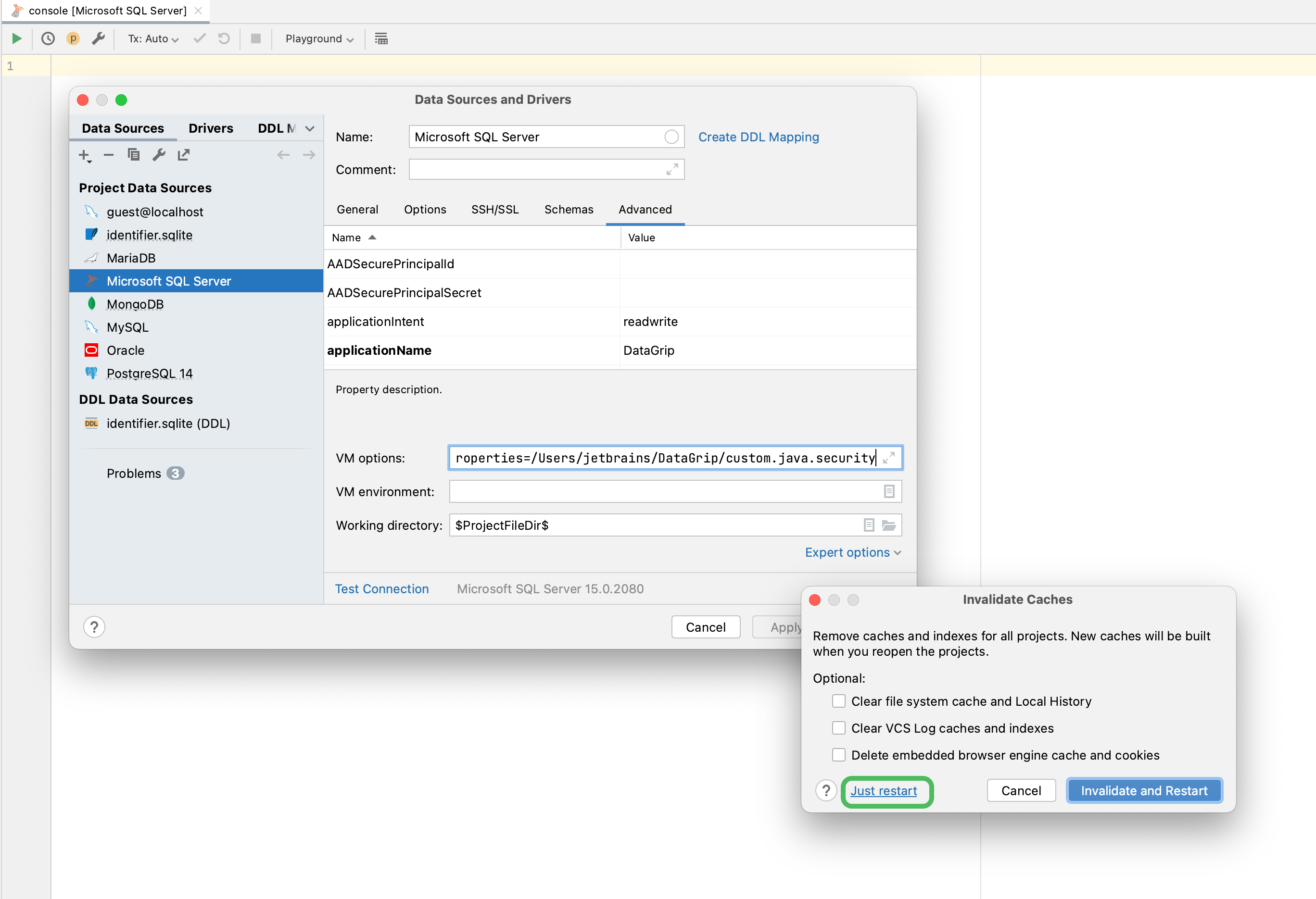
Select your Microsoft SQL Server data source and click the Advanced tab and add the following option to the VM options field:
-Djava.security.properties=${PATH_TO_FILE?}/custom.java.security, where${PATH_TO_FILE?}is a path to the created custom.java.security file.Go to File | Invalidate Caches | Just restart.
Try to connect to your Microsoft SQL Server data source.
Thanks for your feedback!