LDAP Auth Module
An LDAP authentication module lets users log in to Hub and any connected services with credentials that are stored in a directory service. This authentication module is pre-configured for LDAP. You can configure a module to use the standard LDAP scheme or LDAPS over SSL.
The LDAP authentication module does not import all the user accounts from the directory service. Hub only creates a user account when an unregistered user first logs in to Hub or a connected service.
When LDAP authentication is enabled, Hub checks the directory service for each login attempt. Users who have been removed from the directory service cannot log in to Hub.
Prerequisites
If you want to connect to the directory service over SSL, import the trusted SSL certificate for your LDAPS server before you enable the authentication module. If there are any intermediate certificates that sit between the SSL certificate and the root CA certificate, you need to upload a file that contains the full certificate chain.
The option to import a trusted SSL certificate is not supported in the settings for the LDAP authentication module. Instead, you need to access the Trusted SSL Certificates page and import it there. For more information, see Trusted SSL Certificates.
Enable LDAP Authentication
To allow users stored in a directory service to log in to Hub, enable an LDAP authentication module.
To enable LDAP authentication:
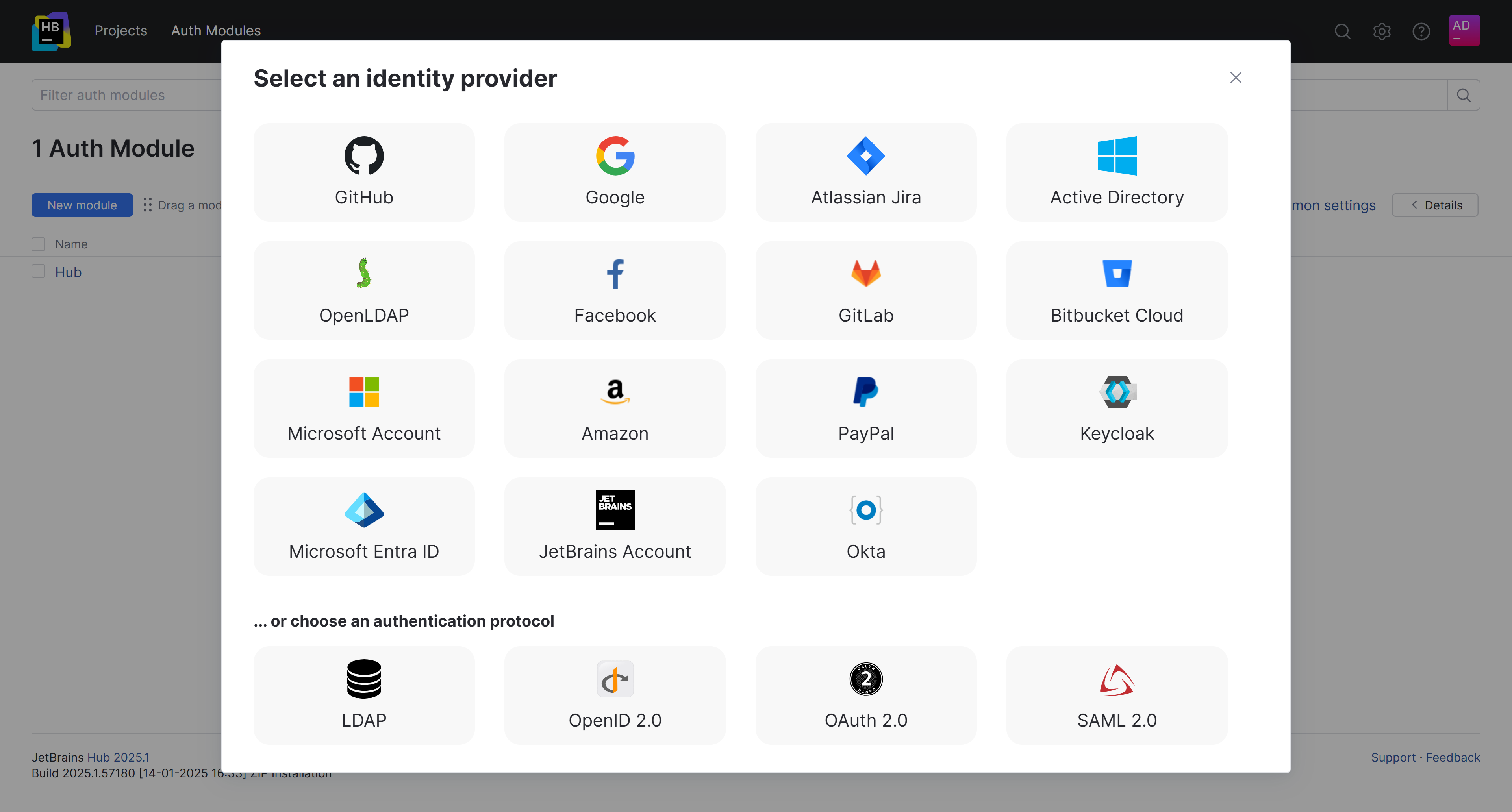
From the main navigation menu, select Auth Modules.
Click the New module button.
In the Select an identity provider dialog, select LDAP.
In the New LDAP Auth Module dialog, enter values for the following settings:
Setting
Description
Name
Enter a name for the authentication module.
Server
Enter the server address of the directory service. For a connection over SSL, change the protocol part of the address to
ldaps.Port
Enter the number of the port used to communicate with the directory service.
The default port for standard LDAP is
389.The default port for LDAPS is
636.
SSL
Enable this option to connect to the directory service over SSL. Before you can establish a secure connection, you need to import the trusted SSL certificate for your LDAPS server. For instructions, see Trusted SSL Certificates.
Search Base
Enter the domain components that define the top-level LDAP DN where user accounts are stored. For example, if your company uses the domain
mycompany.com, enter the top-level LDAP DNdc=mycompany,dc=com.The value stored in this field is added to the LDAP URL and cannot contain unsafe characters.
If you use organizational units to manage users, create separate auth modules for each organization. Include the organizational unit in the search base to create a unique LDAP URL for each module. LDAP authentication modules do not support recursive search in the LDAP tree.
Click the Create button.
The LDAP authentication module is created. The current status of the module is displayed next to the name of the module in the header.
The Auth Modules page displays the settings for the LDAP authentication module. The module is pre-configured with standard settings that are based on the information you provided in the Add Module dialog. For additional information about the settings on this page, see the Settings section.
To complete the setup:
Configure the optional settings for the authentication module. For more information, see Additional Settings.
Click the Save button to apply the settings.
Click the Enable button.
The LDAP authentication module is enabled.
The icon stored in the Button image setting is added to the login dialog window. Users can click this icon to log in to Hub with their LDAP credentials.
Test the Connection to your Directory Service
To verify that the LDAP authentication module is connected to your directory service, test the connection.
To test the connection:
Click the Test login button.
In the Test Authentication dialog, enter the credentials of a user who is stored in your directory service:
In the Username field, enter the
domainusername.In the Password field, enter the
password.
Click the Test login button.
Hub searches for the specified user account in the directory service. If the user is found, a success notification is displayed. If you get an error, check your user credentials and server URL.
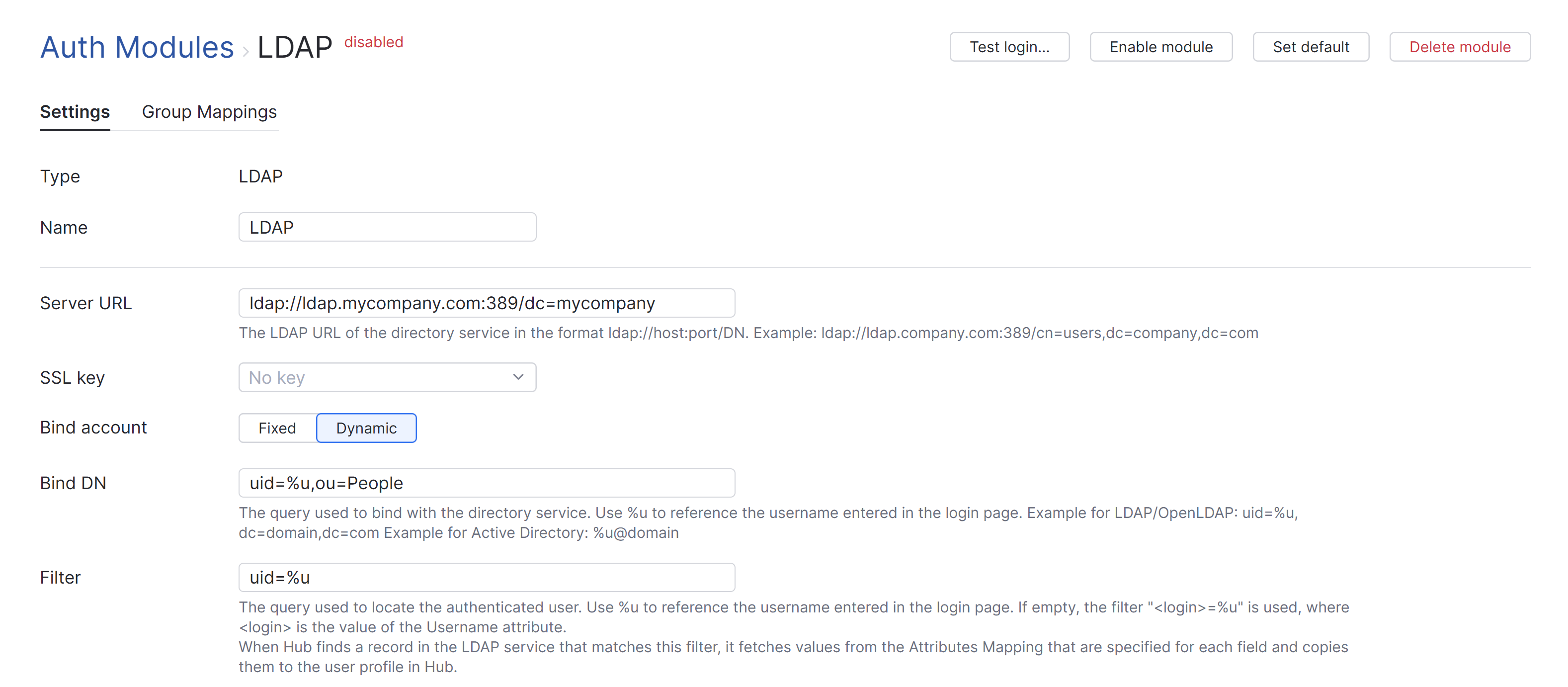
Settings
Use the following settings to fine-tune the connection to your directory service.
Field | Description | ||||||
|---|---|---|---|---|---|---|---|
Type | Displays the type of directory service that is enabled for third-party authentication in Hub. | ||||||
Name | Stores the name of the authentication module. Use this setting to distinguish this module from other authentication modules in the Auth Modules list. The name is also shown in the list of supported authentication providers on the login form. | ||||||
Server URL | Stores the LDAP URL of the directory service used to authenticate a login request in Hub. The LDAP URL uses the format | ||||||
SSL key | Selects an SSL key that can be used to verify the identity of your Hub installation to the LDAP service. You should only need to use this setting when your LDAP service requires client SSL authentication. This list displays only keystores that have been imported into Hub. For more information, see SSL Keys. | ||||||
Bind account | Determines which account is used for the LDAP bind request. For more information, see Bind Account Options. | ||||||
Bind DN | Stores the value used to bind with the directory service. For more information, see Bind Account Options. | ||||||
Filter | Stores an expression that locates the record for a specific user in the LDAP service. The substitution variable in the expression is replaced with the value entered as the username or email on the login page. | ||||||
LDAP referral | Determines whether the LDAP authentication module ignores or follows requests from the service to locate additional information in the LDAP directory.
| ||||||
LDAP account status | Determines whether user accounts statuses are updated in Hub when an account with corresponding credentials is deleted from the connected directory service.
The following options are available for this setting:
This setting is only available when the Bind account setting for the authentication module is set to Fixed. If the Synchronization setting is On, the account status is updated at the predefined interval. Otherwise, the account status is only synchronized when users attempt to use their LDAP account to log in to an application through Hub. | ||||||
Synchronization | Determines the frequency with which user account credentials and group memberships are synchronized with the directory service. You can choose from one of three predefined intervals:
You can also manually synchronize the Hub database with the directory service at any time by clicking the Synchronize now button. Values for the Full Name, Username, and Email that are stored in the Hub profile are populated when the user account is first created, which is usually when a new user logs in to Hub using their Okta account. Later changes to these attributes in Okta profiles are not synced with the Hub profile. These changes are synced with the corresponding attributes that are associated with their Okta credentials. This information is displayed in the Credentials section of the Account Security tab in the Hub profile. This synchronization applies to the attributes that are configured in the Attribute Mapping settings and group memberships as configured on the Group Mappings tab. For details, see Attribute Mapping and Group Mappings. When synchronization is Off, group memberships and account statuses are still synchronized on a per-user basis during login. To learn more about this feature, see Group Mappings. The Synchronization option is only available when the Bind account setting is Fixed. This allows Hub to search the directory service on behalf of the bind account owner. The synchronization feature is only active when the authentication module is Enabled. |
Bind Account Options
You can configure the module to perform the bind request with the LDAP service in one of two ways. The method used is determined by the option selected for the Bind account setting.
The value that you use for the Bind DN setting depends on the option that you select for the Bind account setting. Use the following guidelines to set the value for the Bind DN setting:
Option | Description | Guideline for Bind DN Setting |
|---|---|---|
Fixed | Uses a fixed account to bind to the LDAP service and searches for the user you want to authenticate on behalf of the bind user. With this option, you can set up an LDAP authentication module and still use logins that are not part of the Distinguished Name (DN), like an email address or token. This method is also commonly called search + bind or two-step authentication. To use this method, you need a special account on the directory server that has permission to look up other user accounts in the directory service. | Enter the full DN of the user account that you want to use for the LDAP bind request. This account must have permission to look up other user accounts in the directory service. Use the Change password control to store the password for this account in Hub. The password for the bind user is stored as a salted hash of the plain-text value. |
Dynamic | Derives the user DN from the login and attempts to bind to the LDAP service as the user directly. This method is also commonly called direct bind. | Use a query to bind with the directory service. This query looks up the distinguished name of the user to be authenticated. Reference the username with an expression. The expression maps a substitution variable to the attribute that stores the username in the directory service. The attribute you select determines which query is used in the filter string. The value entered as the username on the login page is trimmed before it replaces the substitution variable. If the user specifies a domain, it is discarded. For example, a username with the value |
Attribute Mapping
When Hub finds a record in the LDAP service that matches a filter, it fetches values from the LDAP attributes that are specified for each field and copies them to the user profile in Hub. Use the following settings to define the filter criteria and map attributes that are stored in your directory service to user accounts in Hub.
Field | Description |
|---|---|
Username | Required. Maps to the LDAP attribute that stores the value to copy to the Username field in the Hub profile. For LDAP, the default value is |
Full name | Maps to the LDAP attribute that stores the value to copy to the Full name field in the Hub profile. |
Maps to the LDAP attribute that stores the value to copy to the Email field in the Hub profile. | |
VCS username | Maps to the LDAP attribute that stores the value to copy to the VCS username field in the Hub profile. |
Groups | Maps to the LDAP attribute that stores group membership assignments in the connected directory service. When this value is specified, you can map and sync group memberships in the directory service with corresponding groups in Hub. For details, see Group Mappings. |
Account expired | Maps to the LDAP attribute that stores the expiration date for the account in the connected directory service. |
Account disabled | Maps to the LDAP attribute that stores the date when the user account was disabled in the connected directory service. |
Lockout threshold | Maps to the LDAP attribute that stores the number of attempts that users are allowed to log in unsuccessfully before their account is locked out. |
Lockout time | Maps to the LDAP attribute that stores the date and time when an account was blocked because the maximum lockout threshold was exceeded. |
Lockout duration | Maps to the LDAP attribute that stores the amount of time a user is blocked from logging in to their account after exceeding the lockout threshold. |
Additional Settings
The following options are located at the bottom of the page. Use these settings to manage Hub account creation, group membership, and connection options.
Option | Description |
|---|---|
User creation | Enables creation of Hub accounts for unregistered users who log in with an account that is stored in the connected directory service. Hub uses the email address to determine whether the user has an existing account. All LDAP authentication modules must allow user creation. If user creation is denied, unregistered users are shown an error. |
Auto-join groups | Adds users to a group when they log in with an account that is stored in the connected directory service. You can select one or more groups. New users that auto-join a group inherit all the permissions assigned to this group. We recommend that you add users to at least one group. Otherwise, a new user is only granted the permissions that are currently assigned to the All Users group. |
Connection timeout | Sets the period of time to wait to establish a connection to the authorization service. The default setting is 5000 milliseconds (5 seconds). |
Read timeout | Sets the period of time to wait to read and retrieve user profile data from the authorization service. The default setting is 5000 milliseconds (5 seconds). |
Audit | Links to the Audit Events page in Hub. There, you can view a list of changes that were applied to this authentication module. |
Group Mappings
On the Group Mappings tab, you can map existing groups in the LDAP service to the groups in Hub.

If you want to map LDAP groups to Hub groups, you need to specify the Groups attribute that stores LDAP group memberships in the Attribute Mapping section of the settings for this auth module.
When group mappings are configured, Hub checks for LDAP group memberships when users log in with accounts that are managed in the directory service. Hub performs the following operations for each LDAP group that is mapped to a Hub group:
Users who are members of a mapped LDAP group and are not members of the mapped Hub group are added to the group in Hub.
Users who are not members of a mapped LDAP group and are members of the mapped Hub group are removed from the group in Hub.
This behavior is based on the current value for the Synchronization setting.
When the Synchronization setting is On, these operations are performed on a set schedule.
When Off changes to group memberships in the directory service are only applied in Hub when users log in using the LDAP auth module.
Scheduled synchronization is only available when the Bind account option is Fixed. If the Bind account option is Dynamic, group memberships are synchronized only on user login.
You can map multiple LDAP groups to a single target group in Hub. You can't map LDAP groups to more than one Hub group.
To map an LDAP group to a group in Hub:
Open your LDAP auth module.
Select the Group Mappings tab.
Click the Add mapping button.
The Add Mapping dialog opens.
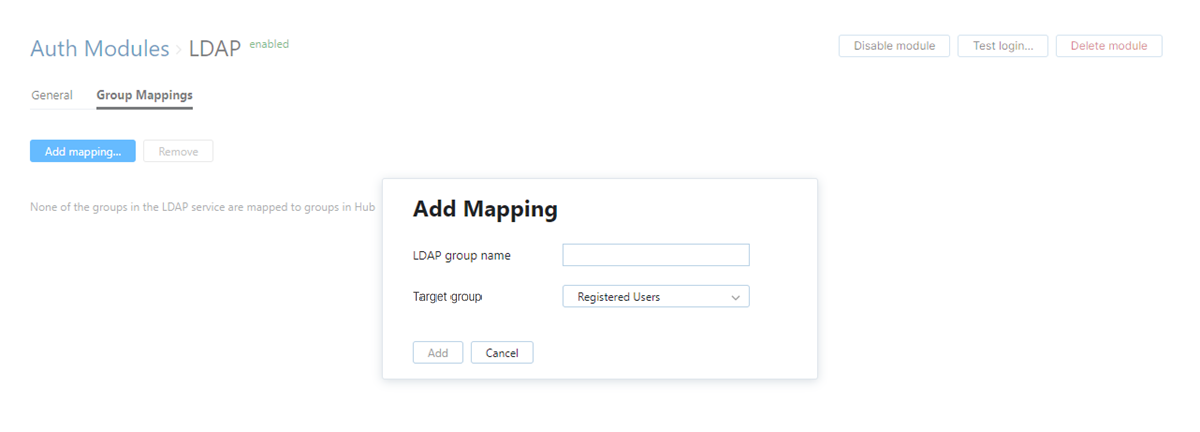
Enter the name of the LDAP group in the LDAP group name field.
If the Bind account option is set to Fixed, the auth module uses the bind account to look up groups in the directory service. Available groups are shown in the LDAP group name list.
If the Bind account option is set to Dynamic, the list of groups in the directory service is not available to the bind account. To map a group successfully, you need to enter the full DN of the group exactly as it appears in the directory service.
Select a group from the Target group list.
Click the Add button.
The mapping is added to the list.
Actions
The following actions are available in the header:
Action | Description |
|---|---|
Set default | Designates the authentication module as the default for your installation. Only one authentication module can be set as the default at any time. If another module is currently set as the default, that state is cleared. This option is only shown when the current authentication module is not designated as the default. |
Clear default | Removes the authentication module as the default for your installation. If none of the available authentication modules are designated as the default, unauthenticated users are always directed to the Hub login page. This option is only shown when the current authentication module is designated as the default. |
Disable module | Disables the authentication module. This option is only shown when the authentication module is currently enabled. |
Enable module | Enables the authentication module. This option is only shown when the authentication module is currently disabled. |
Test login | Lets you enter a username and password to test the connection with the authentication service. |
Delete module | Removes the authentication module from Hub. Use only when you have configured additional authentication modules that let users log into your Hub installation. |
Sample Configurations
Use the following patterns to configure an LDAP auth module using the LDAP protocol:
Setting | Value |
|---|---|
Server URL |
|
Bind DN |
|
Filter |
|
Use the following patterns to configure an LDAP auth module with a secure connection over SSL:
Setting | Value |
|---|---|
Server URL |
|
Bind DN |
|
Filter |
|
Troubleshooting
If you encounter problems with this authentication module, see if the following condition applies.
Condition — Group memberships are not properly synchronized with the directory service, or synchronization is applied inconsistently.
Cause | Solution |
|---|---|
The Hub user account stores credentials for multiple accounts that are managed in the directory service. The accounts in the linked directory service belong to different sets of groups. If a Hub user has multiple accounts that are managed in the linked directory service, group membership synchronization may behave unpredictably. The synchronization job will apply membership assignments for the first account it finds, then update these assignments if it encounters different group assignments for subsequent accounts. | You can resolve this problem by applying any one of the following solutions:
|