Inspect open-source projects
Edit page Last modified: 07 February 2023This section explains how you can inspect your open-source projects using Qodana, and how you can use Qodana Cloud to overview Qodana inspection results in a convenient form and free for open-source projects.
Before you start
Make sure that you already know how to:
Inspect your code using Qodana
Configure Qodana using
qodana.yamland Docker image configurationBuild Qodana into your CI/CD pipelines
Forward reports to Qodana Cloud
Create an account and projects in Qodana Cloud
Qodana Cloud provides two account types suitable for inspecting open-source projects:
Personal account to let you inspect your pet projects; however, it is restricted to a single user and the user's personal organization
Account for open-source projects to let you create organizations and teams, and share inspection results with your peers
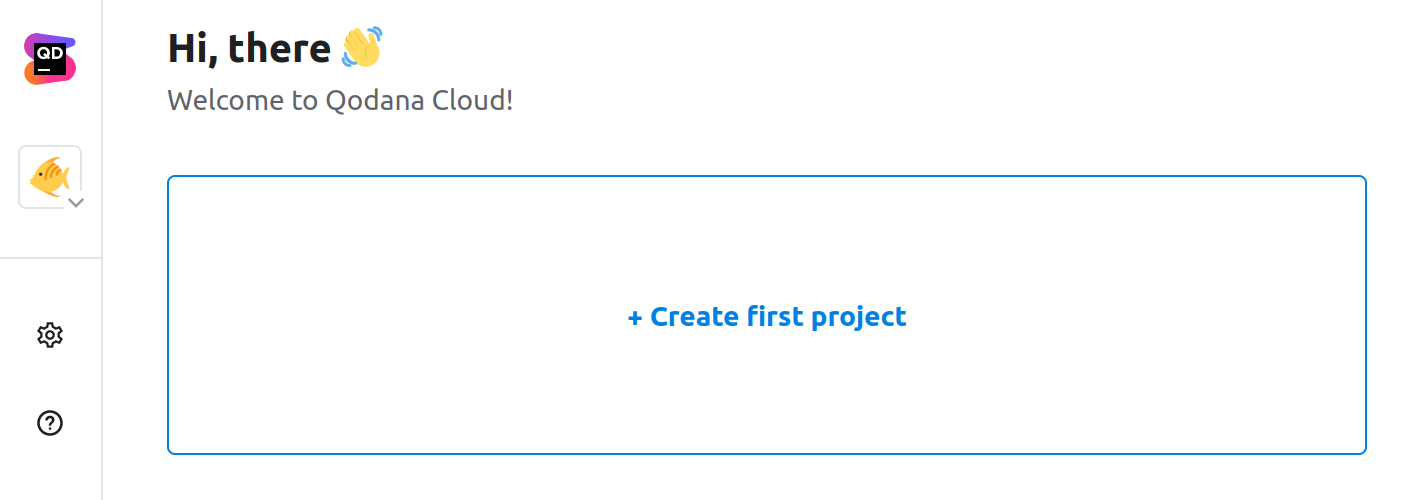
If you would like to use your personal account and a personal organization, on the organization page, click the Create first project button.
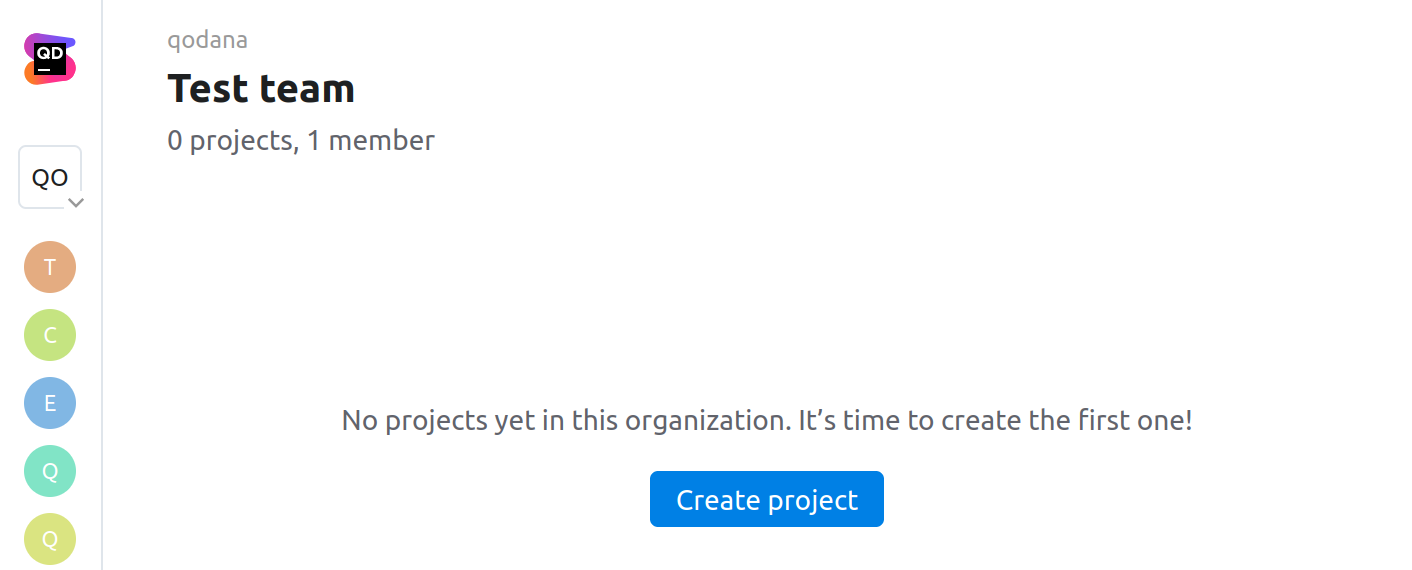
If you would like to overview Qodana reports using your open-source account, you need to create your own organization and a team, or navigate to the team of an existing organization you wish to create a project under. On the team page, click the Create project button.
After the project was created, you can generate a project token to uniquely identify the project. To do this, click Generate token.
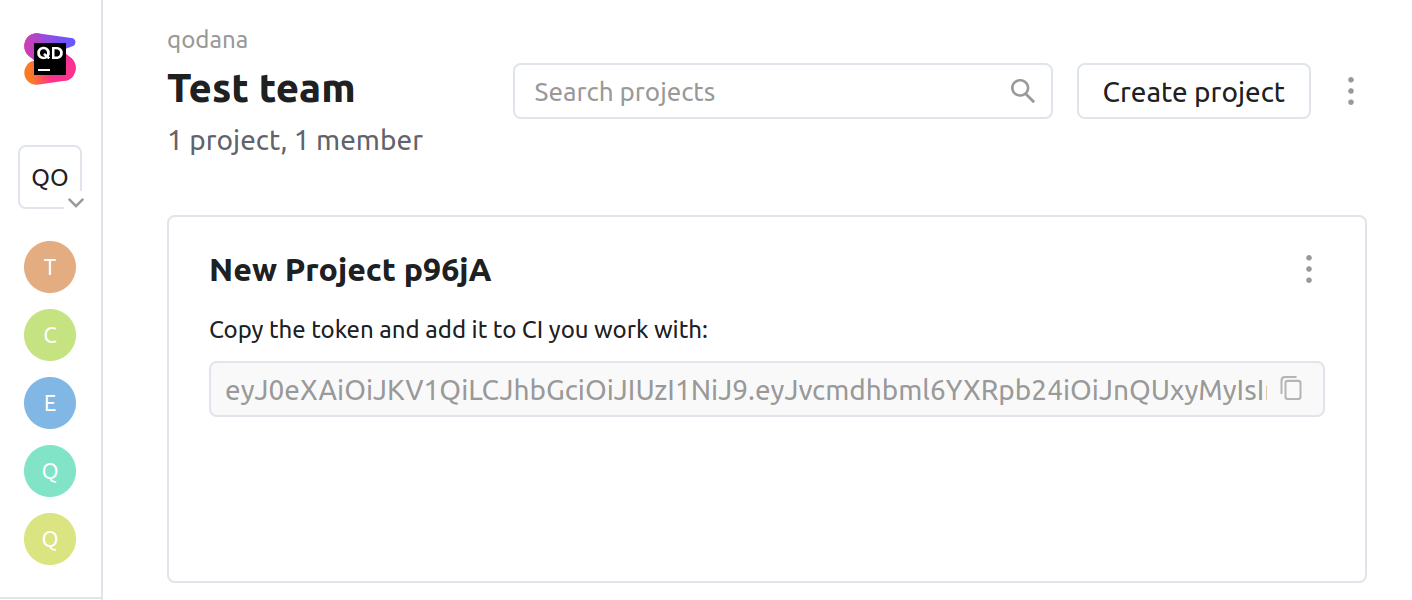
To learn more about using project tokens, see the Forward reports section.
Inspect your projects
You can inspect your codebase using methods described on this page. Additionally, you can configure:
Inspections that you would like to use
License audit for checking license compatibility
Baseline for monitoring current and new problems
Quality gate for restricting the number of problems
Configure inspections
By default, Qodana inspects your code using the qodana.starter profile. You can use additional inspections by specifying the qodana.recommended profile in the qodana.yaml file contained in your project root:
profile:
name: qodana.recommendedTo check the overall configuration of your project, you can employ the qodana.sanity profile:
profile:
name: qodana.sanityConfigure License audit
License audit lets you track compatibility of dependency licenses with your project license.
To enable License audit, add these lines to the qodana.yaml file in your project root:
include:
- name: CheckDependencyLicensesConfigure baseline
Baseline lets you create a snapshot of your project that will be used as a basis for subsequent analysis. To enable it, select inspections and download the qodana.sarif.json file.
You can run Qodana with the baseline enabled using the --baseline option:
−−baseline <path-to-qodana.sarif.json>Configure quality gate
Quality gate lets you configure the ultimate number of problems that will cause a CI/CD pipeline failure.
Once configured, the quality gate will make your CI/CD system:
Build the project only if the number of problems contained in it is below the configured threshold
Accept only the pull requests containing problems below the configured threshold
To enable the quality gate, you can use the fail-threshold <number> option.
Types of Qodana reports
Qodana can generate the following types of inspection reports:
Reports containing inspection results over a specific branch of your project
Pull or merge request inspection reports generated by GitHub Actions and GitLab CI/CD
GitHub Actions
Using this example, you can configure GitHub for:
Forwarding inspection results to Qodana Cloud
Blocking the merge of pull requests if the quality gate has failed
Follow these steps:
Create an encrypted secret with the
QODANA_TOKENname.Create a new or open an existing GitHub workflow that invokes the Qodana Scan action.
Set the workflow to run on
pull_requestevents that target themainbranch, and forward reports based on theQODANA_TOKENvalue. Instead ofmain, you can specify your branch here.
name: Qodana
on:
workflow_dispatch:
pull_request:
branches:
- main
push:
branches:
- main
- 'releases/*'
jobs:
qodana:
runs-on: ubuntu-latest
steps:
- uses: actions/checkout@v3
with:
fetch-depth: 0
- name: 'Qodana Scan'
uses: JetBrains/qodana-action@v2022.2.3
env:
QODANA_TOKEN: ${{ secrets.QODANA_TOKEN }}Set the number of problems (integer) for the Qodana action
fail-thresholdoption.Under your repository name, click Settings.
On the left menu, click Branches.
In the branch protection rules section, click Add rule.
Add
mainto Branch name pattern.Select Require status checks to pass before merging.
Search for the
Qodanastatus check, then check it.Click Create.
GitLab CI/CD
Using this example, you can configure GitLab CI/CD for:
Inspecting the
mainbranch and all merge requestsBlocking merge requests if the quality gate has failed
Forwarding inspection results to Qodana Cloud
Follow these steps to add a Qodana runner to a GitLab CI/CD pipeline:
Create the
QODANA_TOKENvariable and save the Qodana Cloud project token value in itPaste this sample to the
.gitlab-ci.ymlfile:
stages:
- qodana
qodana:
stage: qodana
only:
- main
- merge_requests
image:
name: jetbrains/qodana-<linter>
entrypoint: [""]
script:
- qodana --save-report --results-dir=$CI_PROJECT_DIR/qodana
--report-dir=$CI_PROJECT_DIR/qodana/report
--fail-threshold <number>
artifacts:
paths:
- qodanaIn this sample, specify the Qodana linter and the quality gate using --fail-threshold option. Using this configuration, Qodana will inspect the main branch and all merge requests coming to your repository.
Overview inspection results
After your project is inspected and inspection results are uploaded to Qodana Cloud, you can overview results as shown on this page.
Thanks for your feedback!